Security
What we're doing
In order for you to be safe, we have taken the necessary steps to ensure a secure Internet banking environment.
Immediate access block
Internet firewall
You can block your photoTAN yourself in our Online Banking. The block is effective immediately. For security reasons, we recommend that you block your photoTAN procedure in the following cases:
• Smartphone lost or sold.
• Suspected misuse.
In Online Banking
1. Log in to access your TAN settings.
2. Click on "Manage" in the "photoTAN" line.
3. Then click twice on the "Block photoTAN" button to confirm the blocking of the photoTAN procedure.
Note: If you are using several user numbers, carry out the process separately for each user number as described above.
On the phone
1. Get in touch with us. You can reach us around the clock: 24 hours - 7 days - worldwide.
2. Your photoTAN will be blocked by an employee.
Online applications are authenticated
When you connect to a Commerzbank online application, the Commerzbank system automatically identifies itself by means of a certificate issued by an independent authority. Your computer verifies the authenticity of this certificate before sending data to the Commerzbank system. The certificate guarantees that you are genuinely connected to the online system of the Commerzbank.
Authorising the access
In order to use online applications you must first log on. To do this you must enter your user ID or user name together with your PIN code or password. This identifies you as the genuine user and ensures no one else can obtain access to your data. If the logon details are keyed in incorrectly three times in succession, access to the online account is automatically disabled.
Confidentiality of data transfer, data integrity
All communication between your computer and the Commerzbank online applications is encrypted. The keys used are known only to your computer and to the Commerzbank system. For eavesdroppers, an encrypted message is no more than a string of apparently random characters.
The encryption prevents anyone other than you from deliberately changing the messages. And the Secure Socket Layer protocol in the online banking system effectively puts a stop to the possibility of strings being manipulated by random (“blind”) alteration of characters.
All transactions must be authorised
Each and every transaction has to be authorised by you. There are various methods of authorisation used by the Commerzbank online applications.
In the payment application Global Payment Plus, you authorise transactions with a digital signature which is read out for this purpose by means of your personal signature card using a USB stick. Please take care that your signature stick with the signature card as well as the related PIN are not accessible to other persons.
Only one session possible
The security concept ensures that only one session under your user ID may be active at any one time. If there is an extended period without activity during a session, the session is automatically closed down. The same applies if the connection between your computer and the application fails for any reason: the session is automatically terminated.
Commerzbank supports TLS 1.2 or TLS 1.3
Communication between your computer and the Commerzbank server is based on the Secure Socket Layer protocol (SSL).
What you can do
We need your help to protect you. Always be vigilant when it comes to your online banking.
Keep your PIN and TANs secret
Anyone who knows your user ID and PIN can log on under your name. And if such individuals also know your transaction numbers (TANs), they will be able to debit payments from your accounts and portfolios. So please observe a few simple rules:
- Do not tell anyone the PIN for your online applications. No Commerzbank employee will ever ask you for your PIN or request you to e-mail this number or other personal data such as your name, address or account number.
- Recently there has been a spate of fraudsters sending e-mails from the address of bona fide companies to request the recipients to log on to a particular web site by clicking a link in the mail. These e-mails usually seem highly plausible and the sites are often virtually identical with the genuine articles. Fraudsters use this scam (called “phishing“, or “password fishing”) to obtain access to your logon data. To play safe, never click on links in e-mails that purportedly lead straight to logon pages of the Commerzbank. To log on, always go via the start pages of companyworld, or key in the address directly.
- Be sure to change your PIN periodically.
- Never ever save your PIN and/or TANs on your computer (not even in your finance software).
- If you have reason to think that the confidentiality of your PIN and/or TANs has been compromised, please disable your access at once and notify your Commerzbank branch or the help desk.
- If you know you will not be using the Commerzbank applications for some time, you might prefer to disable your online access as an additional safeguard against unauthorised use.
Check the Internet address
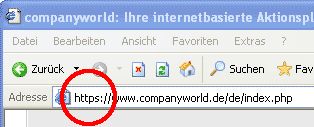
When you launch your online application, always check that you are connected to the right Internet address.
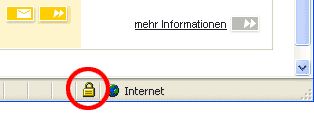
It’s important that the address begins with the protocol https – not http – and that an icon showing a lock is visible in the browser footer line. Do not ever enter your personal data (especially your PIN and password) without first verifying that the address and protocol are correct!
Always end with logout
Each and every transaction has to be authorised by you. There are various methods of authorisation used by the Commerzbank online applications.
In the payment application Global Payment Plus, you authorise transactions with a digital signature which is read out for this purpose by means of your personal signature card using a USB stick. Please take care that your signature stick with the signature card as well as the related PIN are not accessible to other persons.
Check the certificate
Communication between your computer and the Commerzbank server is based on the Secure Socket Layer protocol (SSL).
Browser settings
Always use the latest version of your browser. Up-to-date software will usually have improved security mechanisms. Always close your browser completely after logging off. When working in an alien environment you should play safe and delete the cache completely after use. Follow the instructions in your browser.
Also take note of the recommended browser settings in the installation guide you received with your Commerzbank software.
Protecting against viruses and Trojans
The security concept ensures that only one session under your user ID may be active at any one time. If there is an extended period without activity during a session, the session is automatically closed down. The same applies if the connection between your computer and the application fails for any reason: the session is automatically terminated.
Access from third-party environments
If you use the Commerzbank online applications on computers that are not completely in your control, there are a few additional ground rules you should observe:
- Never leave the computer unattended while an online session is in progress. If you do have to leave the PC, first close the application or activate a password-protected screensaver.
- When entering your PIN, password or TANs, be sure that your keyboard inputs are not being memorised or otherwise recorded by anyone else.
- Protect your TAN list from prying eyes!
- Do not use a computer which can not be trusted. If you use the Corporate Banking portal in a foreign environment, special care must be taken: if you have the slightest doubt about the seriousness of the owner or the system operators of the PC, on no account enter your access data and, in particular, your PIN via such a third-party PC. If necessary, do without access. No one can protect you if, for instance, a program is installed there which intercepts all your entries, including your user number and PIN, and thus makes abuse possible.
- Particularly important: Please ensure that, in a foreign environment, you end every connection with the closed area of the Corporate Banking portal (e.g. Online Banking) with the red “Log off” button provided for this purpose (see also: “Ending an online session”). If possible, do not leave your place at the computer during an active online session. If this cannot be avoided, end your online session beforehand, or at least activate a password-protected screensaver, for which only you know the password. When entering the PIN and TANs, make sure that other individuals do not spy out your keyboard entries. If you use the iTAN method, protect your iTAN lists from prying eyes, and remember too that mini cameras may have been installed.
Latest news
Phishing
How the fraud works:
Internet users get an email that supposedly comes from their bank. Under a pretext, the users are asked to click on a link in the mail to log in to the online banking site.
However, this link leads to a fake website that looks deceptively similar to a genuine site. The user is asked to enter their log in and authorisation data. The input is then misused for illegal purposes by the fraudsters.
How can you protect yourself in this case?
- Firstly, you can be certain that Commerzbank will never ask you to update your personal details by email or ask you to log in online for any other purposes.
- For this reason alone, you can safely ignore such messages. Never use the links in such emails. In case of doubt, contact our Customer Service.
Furthermore, we recommend the following approach to login:
- Type the address manually in the relevant line in your browser software or use a “bookmark” previously saved in your “Favourites” menu.
- Do not use any links sent in emails, even if the message ostensibly comes from a trusted sender.
- Do not complete any electronic forms in emails that include a request to disclose log in data.
- Use an up-to-date browser. Get regular security updates from the producer of your computer operating systems – e.g. for Windows on https://windowsupdate.microsoft.com.
What to do if you are affected:
If you think you have been the victim of a “phishing” message and fraudsters have gained access to your identification data, please do the following:
- If you have revealed your log in data, immediately deactivate access in your Online Banking/Administration service and contact your Commerzbank branch or Customer Service.
You are also welcome to send us your message via fax to the following fax number: +49 (0) 40 - 3 76 95 400.
We also recommend the following procedure to login:
- Key the address in the browser window manually, or use an entry you have previously created in the “Favourites” menu.
- Do not use any links sent in e-mails, even if the mail appears to be from a trusted source.
- Do not fill in electronic forms in e-mails that ask you to provide logon data.
- Use a current browser. You can obtain security updates from the producer of your operating system, for example from https://windowsupdate.microsoft.com for Windows operating systems.
If the worst happens: what to do if you’ve navigated to the link
If you think you’ve fallen victim to a ”phishing” mail and your logon data has been compromised by fraudsters, here’s what to do:
- If you have made your login data known, please immediately disable your access in the Online Banking/Administration menu and contact your Commerzbank branch or the help desk.
Trojans
How the fraud works:
The Trojans (derived from the term “Trojan horse”) disguise themselves as a useful program but run damaging programs in the background, so-called malware. A practical example: A well-known company sends alleged invoice emails to potential victims. This email typically portrays an alarming scenario. The reader is told they will find the reason for a high invoice amount via a link in the attachment. This is intended to induce the recipient to click on the link or open the attachment. As soon as they do so, the malware is installed on their computer.
How can you protect yourself in this case?
- Do not let yourself be caught unawares and do not open any attachments or links in email of dubious origin.
- Be careful with add-ins/plug-ins from unknown producers.
- Regularly update your software and operating systems.
- Set your operating systems so your emails are always checked.
- Regularly scan all the drives on your computer for malware.
- Use a firewall that monitors network traffic.
- Use virus protection software and keep it up-to-date. Set your operating systems so your emails are always checked.